Interactive Brokers LLC is an American multinational brokerage firm. It operates the largest electronic trading platform in the U.S. by number of daily average revenue trades. The company brokers stocks, options, futures, EFPs, futures options, forex, bonds, funds, and some cryptocurrencies.
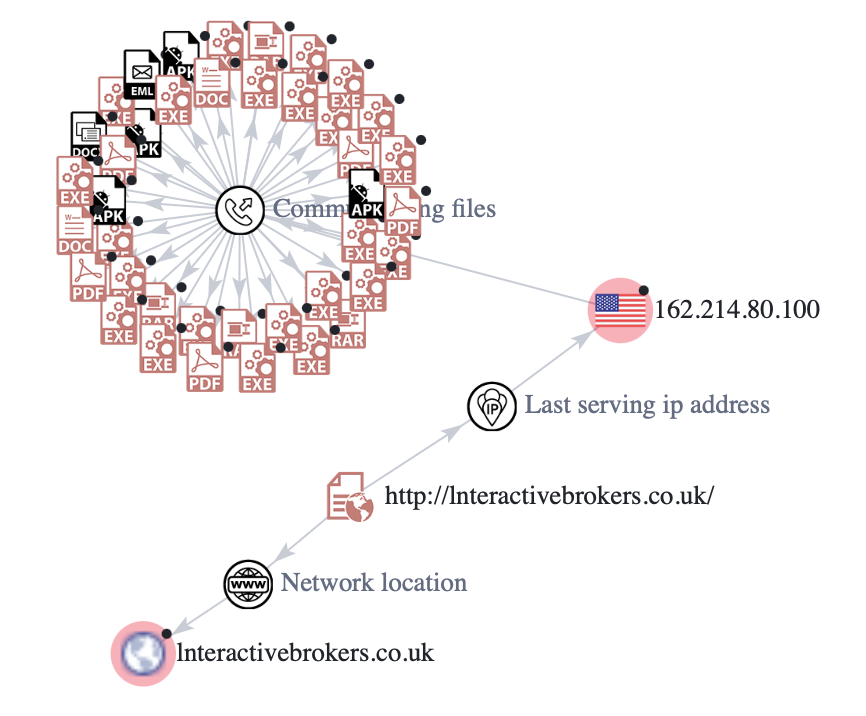
During our PreCrime internet scout of December 8th 2022 we identified suspicious markers across multiple vectors. One of those was this website spoof that could be targeting unsuspecting users of Interactive Brokers.
The Attack
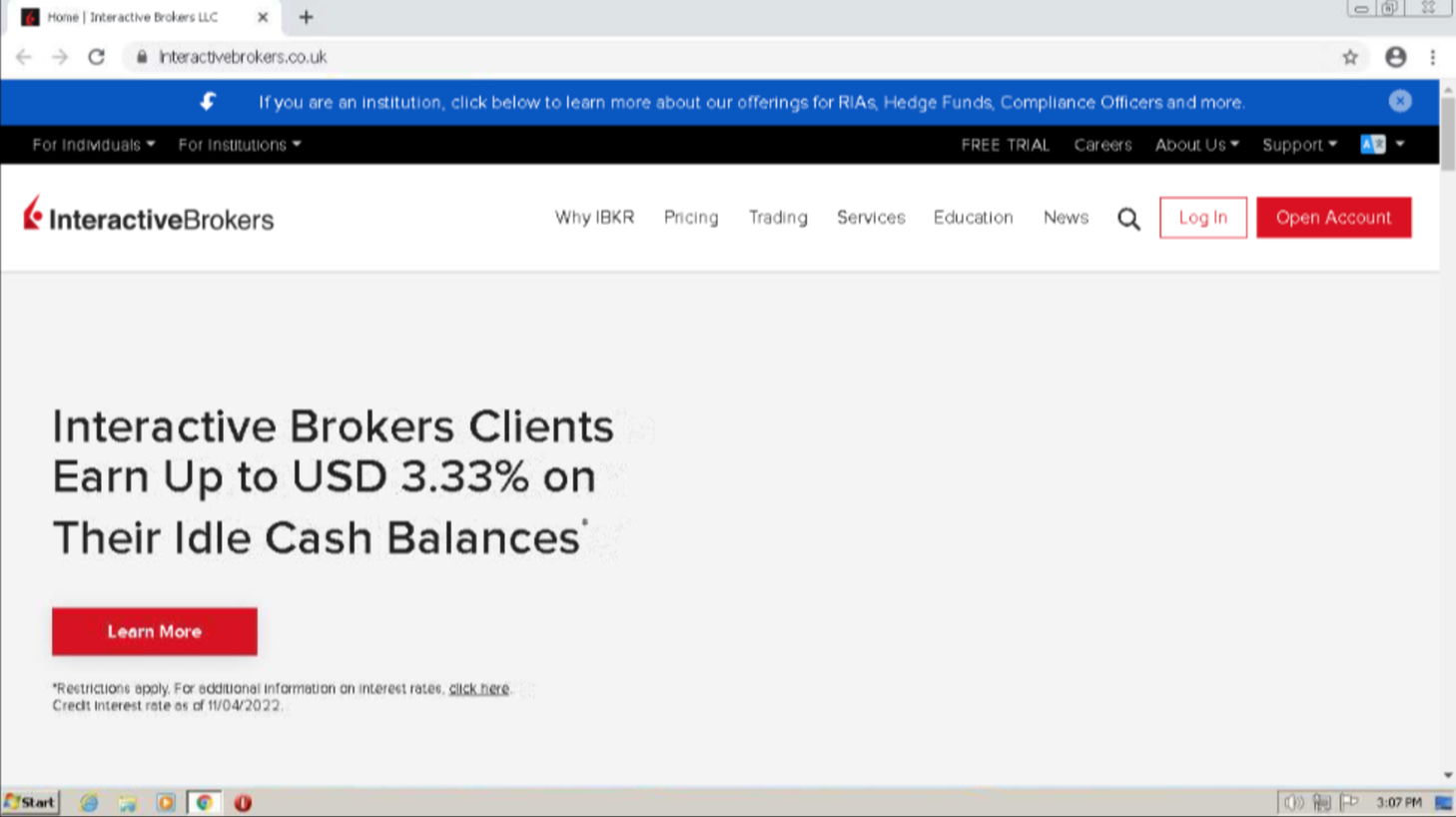
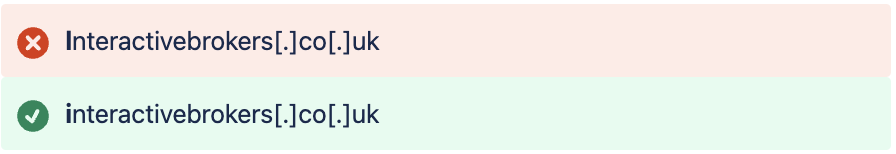
Legitimate site :
interactivebrokers[.]co[.]uk
Malicious domain created on December 7, 2022, identified by Bfore.Ai on December 8, 2022
lnteractivebrokers[.]co[.]uk
This attack shows a brand impersonation attack on Interactive Brokers LLC, an American multinational brokerage firm.
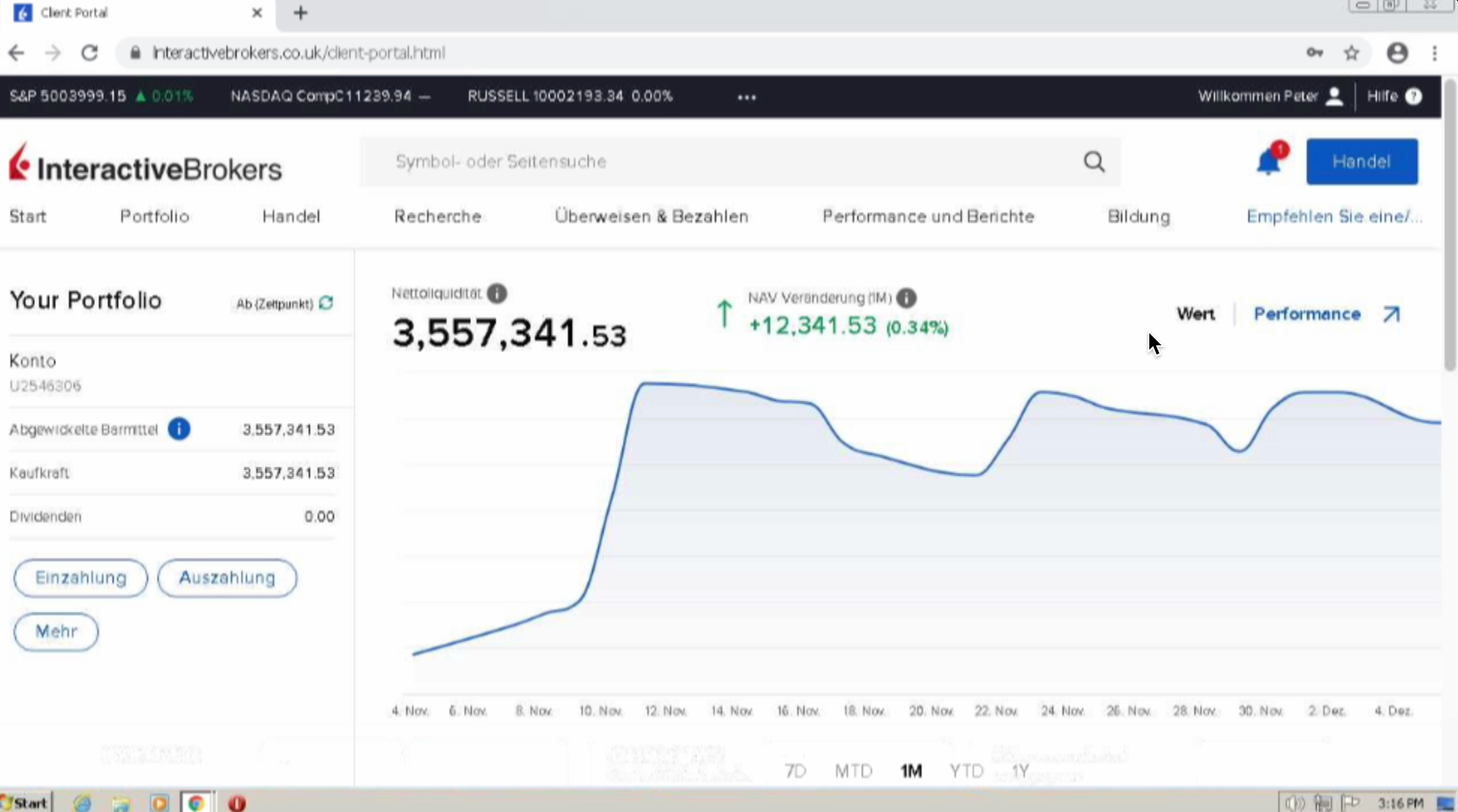
Malicious site
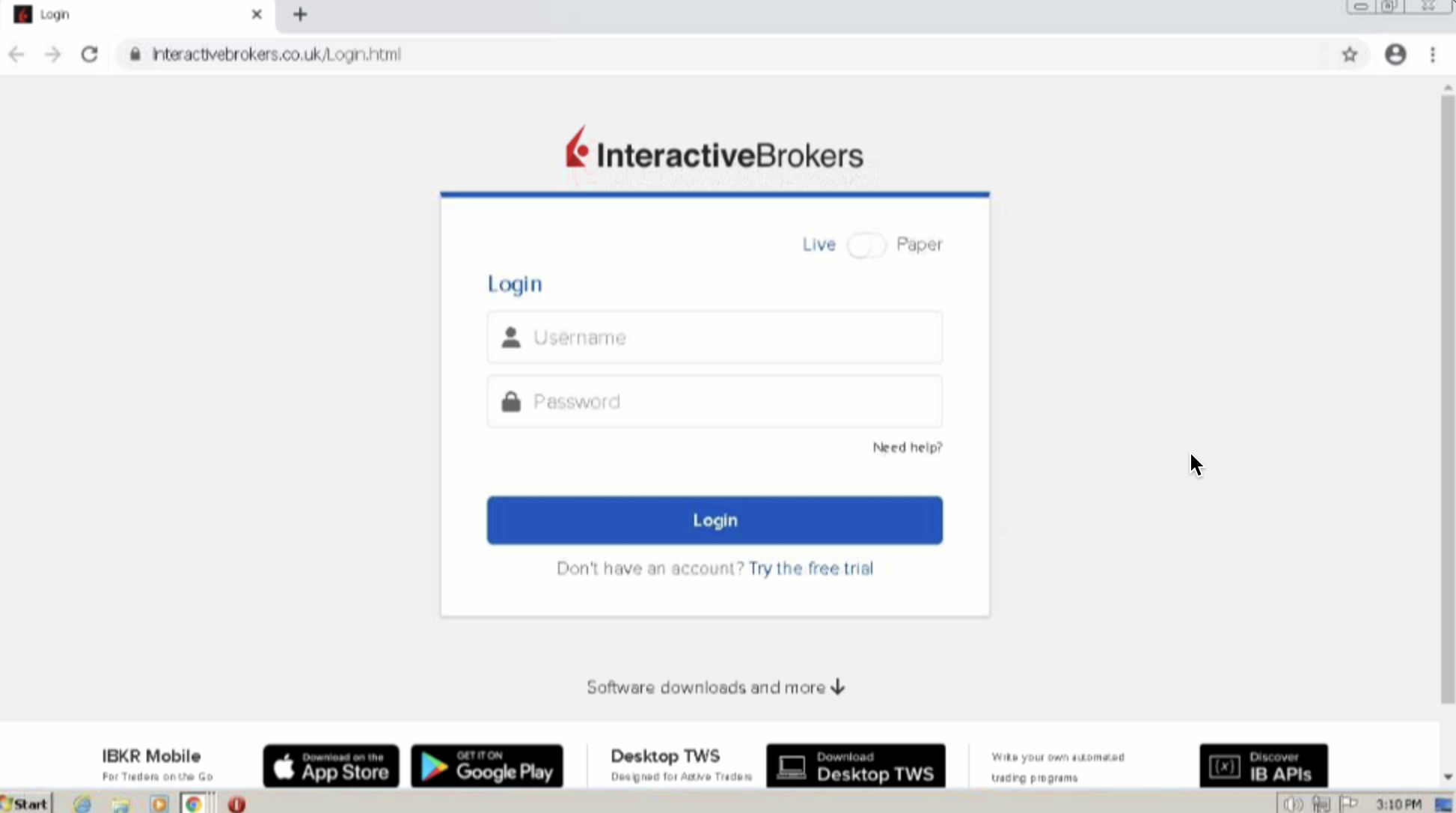
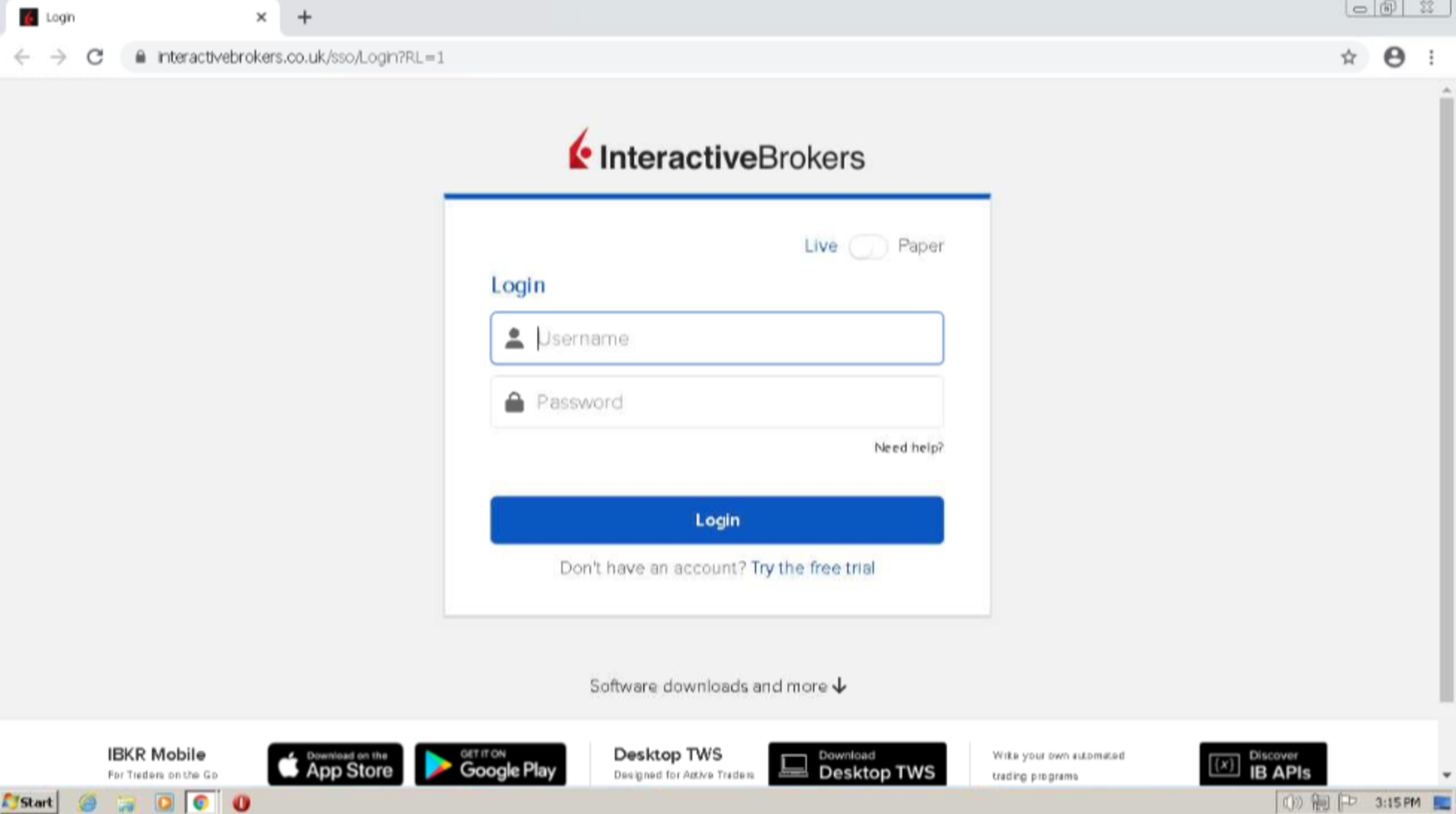
Lead to fake login page
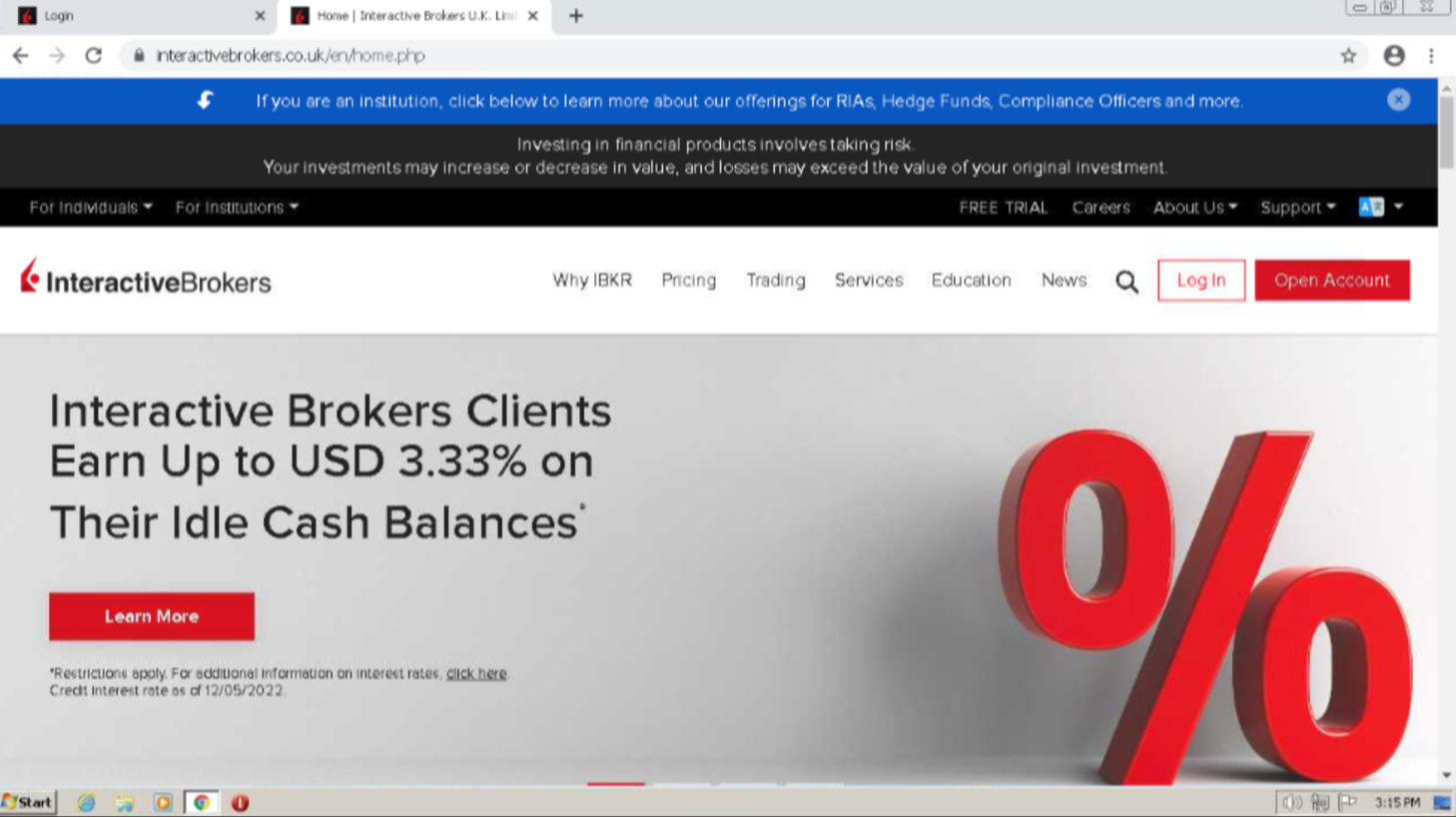
Legitimate site
Legitimate site login page
How does this attack work ?
-
Users may be led to the malicious website through a phishing campaign wherein they are asked to go to the website and log in to their account. The threat actors will likely attempt to entice users into visiting the site by promising them a big cash payout.
-
When opening the malicious domain users are directed to a replica of the legitimate sites home page. The site is almost identical to the malicious site, however with a few noticeable differences. The legitimate site, for example, provides information to users at the top of the page informing them that ‘investing in financial products involves taking risks’, which does not appear on the malicious site.
-
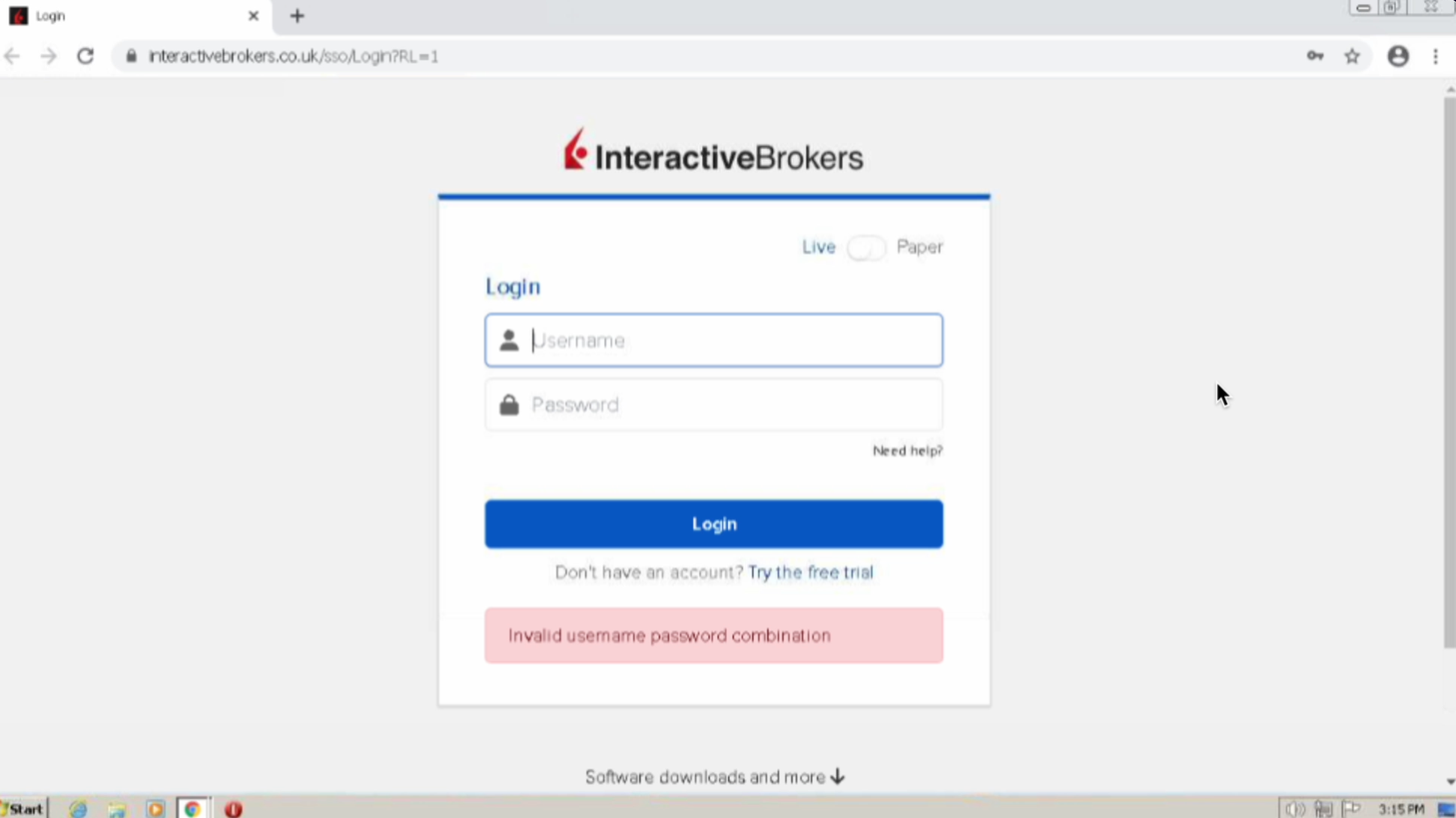
Once users click on login, they are led to a complete replicate of the legitimate sites login page. Users need to provide their username and password. When attempting to login with fake credentials the legitimate site blocks our attempt while the malicious site directs us towards to a website that acts as a client portal (lnteractivebrokers[.]co[.]uk/dient-portal[.]html), where visitors get an overview of a their assets.
Malicious site login attempt
Legitimate site login attempt
On this site, the only link that works is the Auszahlung one, meaning payout. Threat actors are likely attempting to entice users into requesting a monetary payout of their assets which would lead to their bank credentials being stolen.
How do they trick users into believing the attack is real?
-
Using branding from Interactive Brokers including the same logo, colours and font. Additionally, the malicious login page is completely identical to the legitimate one in appearance.
-
Using a domain name similar to Interactive Brokers. The threat actors have replaced the first letter (i) with the letter l (L). See the differences below:
Why is this a threat ?
If successful, this attack would provide threat actors with access to sensitive personal information about the individual or corporate user, allowing threat actors to take control of their bank account and steal their money. Corporations using Interactive Brokers would also be at risk of their internal network being compromised, if their credentials used at Interactive Brokers correspond to those they use for work.
Domain brand impersonation does not just lead to theft of sensitive personal information, but could also result in malware infection for both private consumers and global corporations depending on the target and end goal of the threat actor. This occurs when stolen credentials are sold on the dark web, giving other threat actors the ability to conduct further attacks against the user(s) such as ransomware attacks. Such attacks could pose serious consequences for the company, including high monetary costs, disrupting business operations, exposure of confidential data and reputational damage.
-
A cyber incident of Interactive Brokers could ultimately result in the loss of around 12 million USD.
-
Companies connected to Interactive Brokers could run the risk of a data breach which as of 2022 could result in the loss of around 4,35 million USD.
-
If individual consumers were to become a victim of this attempt to gain their personal information over the internet, they could lose between 2-3 thousand USD.
Recommendations
-
If in doubt whether an email is legitimate, never click on any links. Go to the legitimate website’s domain instead via a search engine.
-
Always double check the domain name to make sure it is the legitimate one.
-
Never use the same credentials for work and personal accounts.
-
Use different passwords for online banking and shopping sites, for example, so if one of your accounts becomes compromised your other accounts will remain safe.
-
Incorporate Multi Factor Authentication where possible to keep your accounts safe even if the credentials are compromised.
Identification and threat analysis
Technical Report
The technical report below helps emphasize the differences in terms of DNS records between the malicious domain, and the legitimate domain.
|
Domain |
lnteractivebrokers[.]co[.]uk |
interactivebrokers[.]co[.]uk
|
|---|---|---|
|
Registrar |
GoDaddy.com, LLC. |
CSC Corporate Domains, Inc
|
|
Name Servers |
ns1.bluehost.in ns2.bluehost.in
|
a28-64.akam.net a10-65.akam.net a26-66.akam.net a11-65.akam.net a1-180.akam.net a9-65.akam.net
|
|
MX record |
lnteractivebrokers.co.uk.
|
primary.us.email.fireeyecloud.com alt1.us.email.fireeyecloud.com alt2.us.email.fireeyecloud.com alt3.us.email.fireeyecloud.com
|
|
Last seen active |
8 December |
8 December |
|
IP address |
162.214.80.100
|
2.16.186.138, 2.16.186.2013 |
|
Domain Age |
1 day old Created 7 December 2022
|
8,966 days old Created 22 May 1998 |
|
Certificate |
Issued by: Let’s Encrypt Issued to: *.lnteractivebrokers[.]co[.]uk Domain validated 07-12-2022 -> 07-03-2023 Valid for 3 months
|
Issued by: DigiCert Inc Issued to: IBG LLC Organisation validated 22-02-2022 -> 22-02-2023 Valid for 1 year
|

How Bfore.Ai is protecting our customers
At Bfore.Ai, we work daily to ensure these phishing attacks get stopped before even reaching their targets. We are here to make your internet journey safer than it has ever been.
With more than 30K new malicious indicators per day we got you covered no matter where the attack comes from. Only 0.05% false positive rate, stop wasting time in false alerts chasing. By launching our PreCrime and PreEmpt technologies, we measure our anticipation from an attack starting, faster than attackers.
Accepting that the only defense is good detection, is accepting to be forever a victim. We believe in prevention more than response. Visit our website for more information !
Appendix
This document and its contents do not constitute, and are not a substitute for, legal advice. The outcome of a Security Risk Assessment should be utilized to ensure that diligent measures are taken to lower the risk of potential weaknesses be exploited to compromise data.
Although the Services and this report may provide data that Client can use in its compliance efforts, Client (not Bfore.Ai) is ultimately responsible for assessing and meeting Client’s own compliance responsibilities. This report does not constitute a guarantee or assurance of Client’s compliance with any law, regulation or standard.



.png)